How To Perform A Cybersecurity Risk Assessment
Updated: May 6,
During a routine SOC 2 audit at a fintech startup, a problem surfaced that nobody saw coming. A former employee’s admin credentials were still active eight months after his last day. Although the ex-employee had never used them, he could have. And the fact that nobody caught it during eight months of normal operations said something uncomfortable about the state of the company’s security program.
This scenario doesn’t draw as much attention as the scary-sounding threats, such as ransomware, nation-state actors, and zero-day exploits. While those threats are real, most breaches trace back to something far less cinematic: an unreviewed access list, a vendor with more permissions than they need, or a critical system nobody thought to put in scope. Boring, fixable stuff that a proper cybersecurity risk assessment identifies before it becomes a headline.
A cybersecurity risk assessment is a structured process for identifying the threats to your IT systems, evaluating how likely they are to materialize, and determining the cost to your business should those threats materialize. For Bay Area startups and SMEs managing sensitive customer data, navigating SOC 2 or HIPAA, or just trying to scale without leaving the door open, a well-executed risk assessment is the foundation everything else builds on.
Here’s how to do it.
What Is a Cybersecurity Risk Assessment?
A cybersecurity risk assessment is a systematic evaluation of your organization’s information systems, the threats that could affect them, and the vulnerabilities that make those threats exploitable. The output is a prioritized, documented picture of your security risk: something you can act on, budget against, and come back to.
It’s really four questions dressed up in a process. What assets do you need to protect? What threats are you actually facing? How exposed are you right now? And what would it cost if something went wrong? Answer those honestly, and you have the raw material for a security program that reflects your real situation, not a generic checklist.
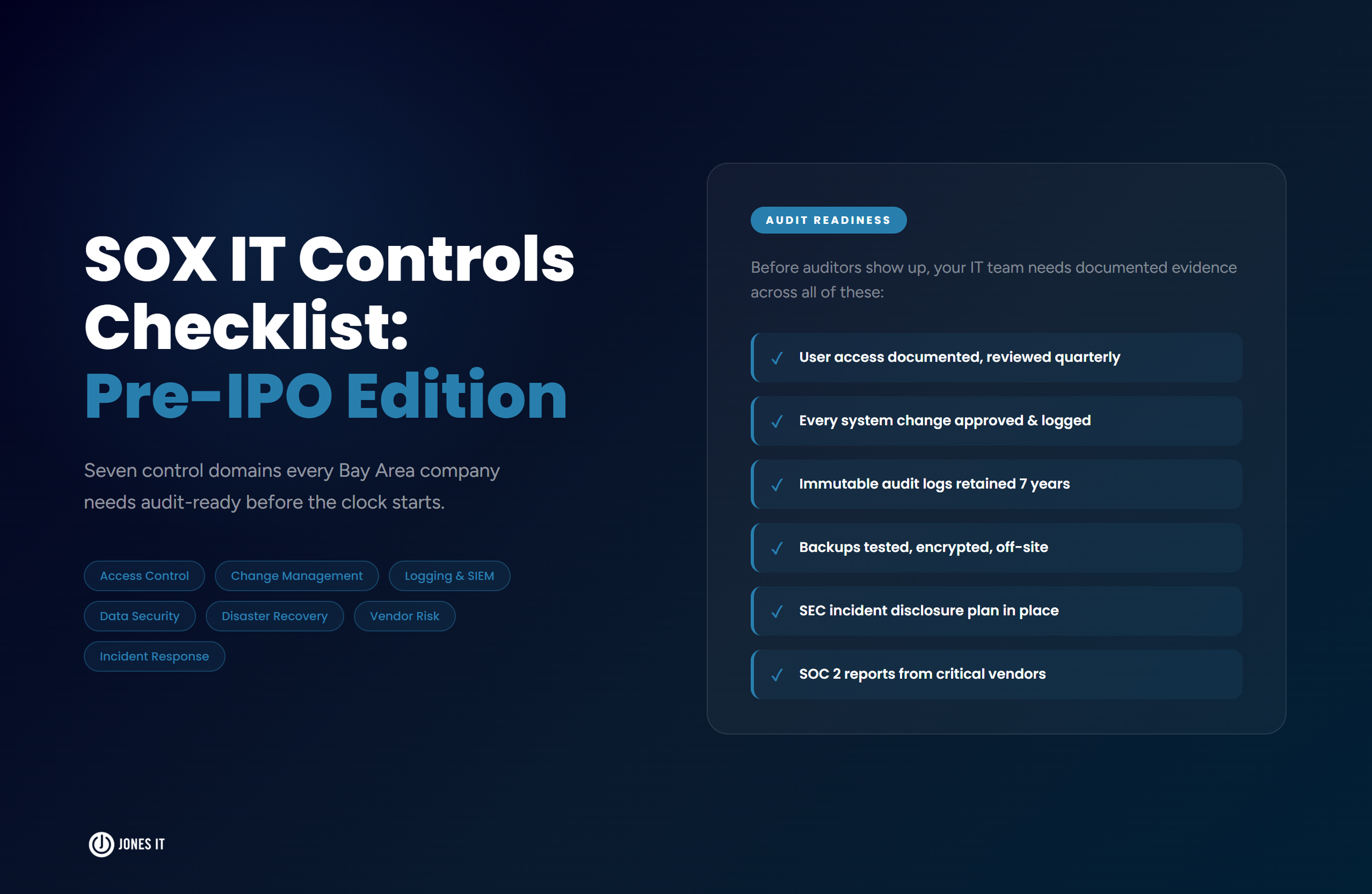
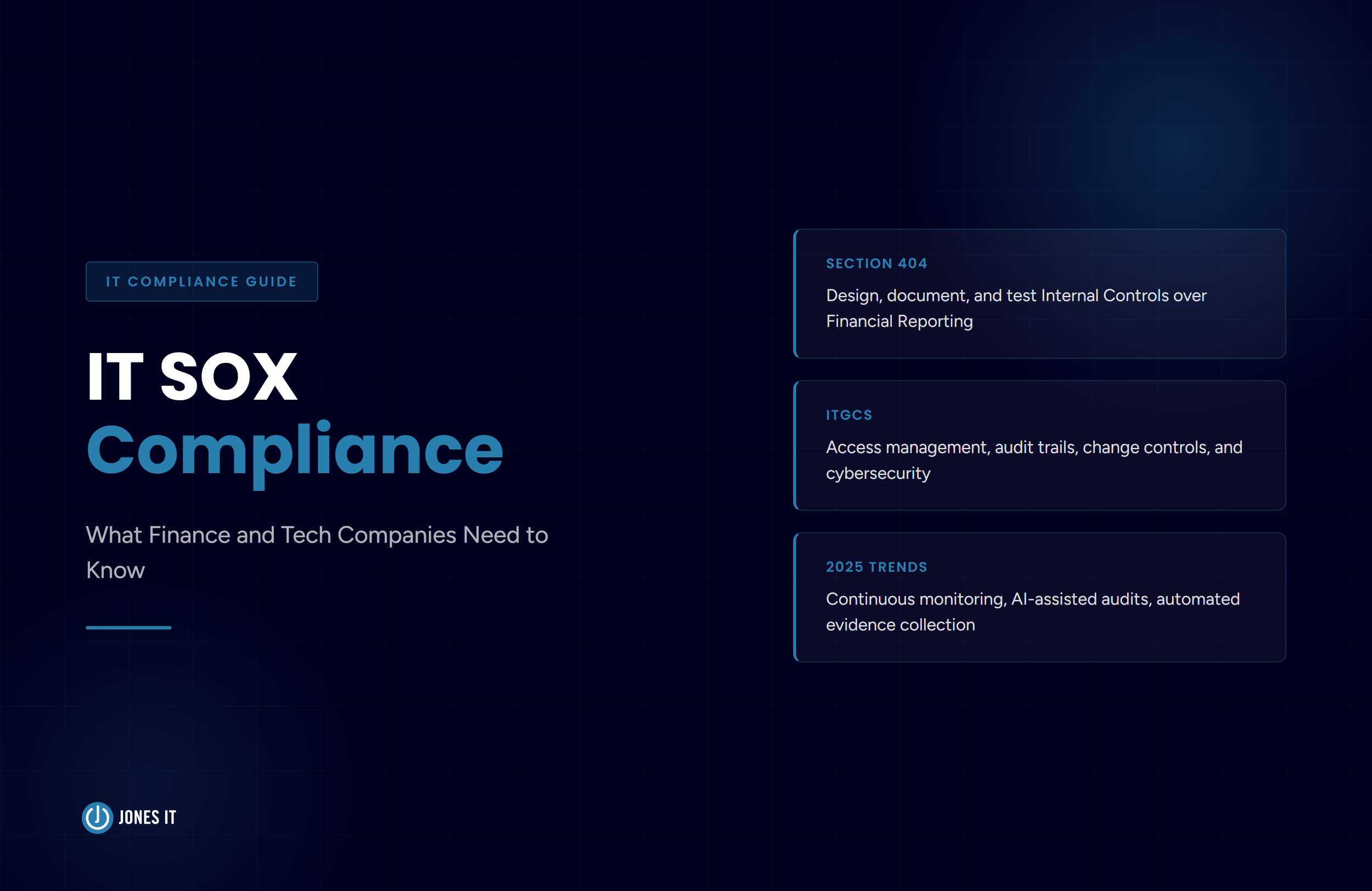
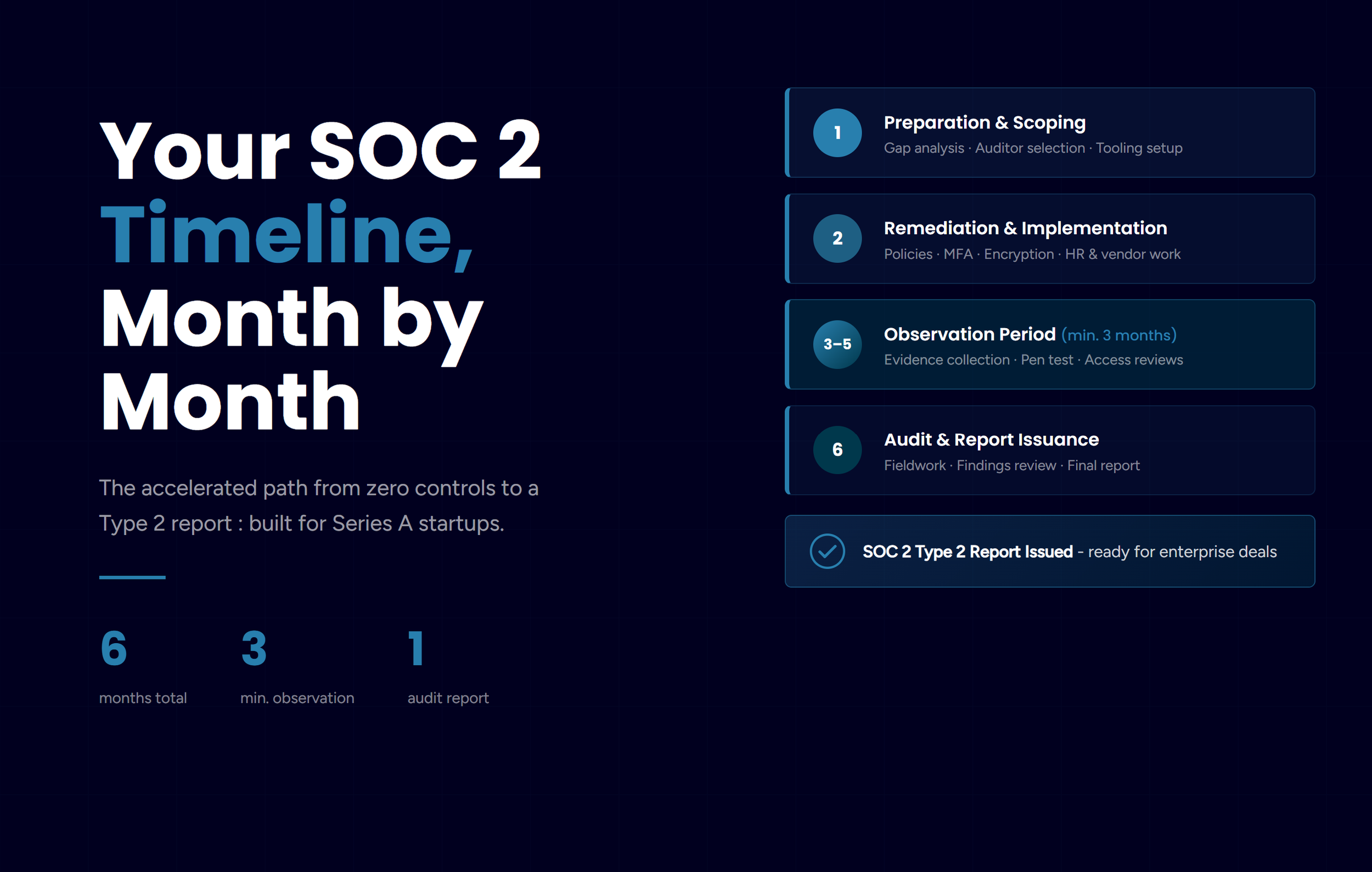
If you’re working toward SOC 2, HIPAA, or ISO 27001 compliance, a risk assessment is not optional. It’s a required step in all three frameworks. But even companies not on a formal certification path get something valuable from the process. They get clarity about where the gaps are and where to spend first.
Why Every Business Needs Regular Cybersecurity Risk Assessments
The word “regular” in that heading is pulling its weight. A risk assessment is not a one-and-done exercise you file away and forget. Your threat environment shifts. Your systems change. People join and leave. Vendors get access. An assessment that was accurate eighteen months ago may have real gaps today, and in security, gaps are the whole problem.
Beyond staying current, there are some hard-nosed reasons to make this a recurring practice:
Cost. Finding and fixing a vulnerability before an incident is almost always cheaper than responding to one after. IBM’s 2025 Cost of a Data Breach Report put the global average breach cost at $4.4 million. Risk assessments let you spend a fraction of that on prevention.
Compliance readiness. HIPAA, SOC 2, ISO 27001, and CCPA all require or strongly imply formal risk management processes. Regular assessments keep your documentation current so audits don’t become fire drills.
Better resource allocation. Security budgets are always finite. A risk assessment tells you where to spend by ranking threats on likelihood and impact, not gut instinct.
Data visibility. For companies handling customer PII, financial records, or protected health information, a risk assessment is often the first time anyone has mapped where that data actually lives, who can access it, and what controls are actually in place around it. The answer is sometimes surprising.
Trust. A breach costs money, yes. It also costs the confidence of customers, partners, and prospective investors. For a Series A or B company in San Francisco or South San Francisco, that trust is often harder to rebuild than the balance sheet.
Our recommendation is to run a full cybersecurity risk assessment at least once a year, and perform one again any time you make a significant infrastructure change, onboard a new critical vendor, or have a compliance audit on the horizon. The cadence matters as much as the process.
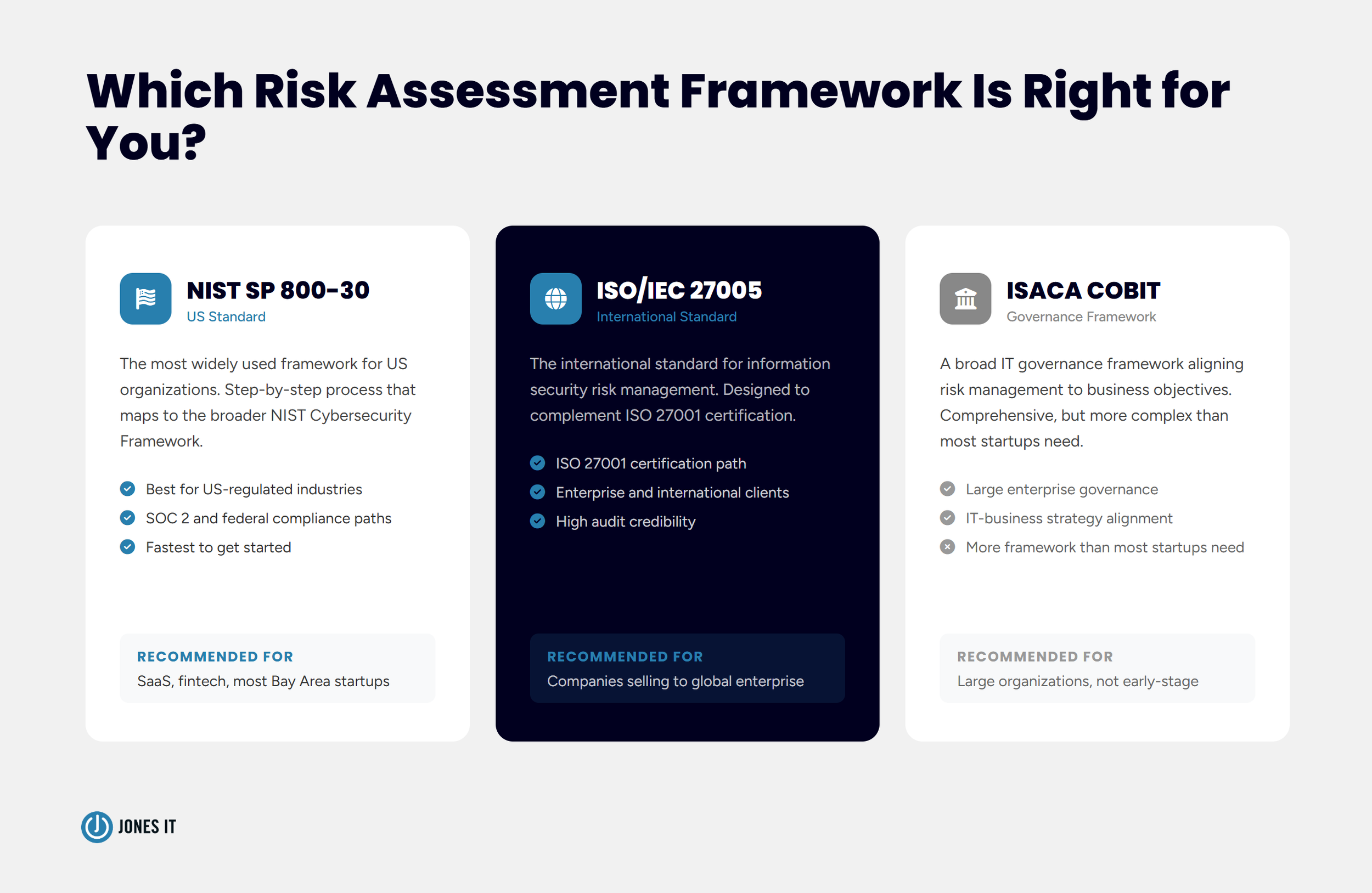
Which Cybersecurity Risk Assessment Framework Should You Use?
Before you start assessing anything, you need a framework. Think of it as the methodology that keeps your assessment consistent year over year, so you’re comparing apples to apples instead of making up the structure as you go. Without one, risk assessments drift. People assess different things in different ways, and the results stop being useful.
Three frameworks dominate for Bay Area businesses:
NIST SP 800-30
The most widely used risk assessment guide for US-based organizations, NIST SP 800-30 gives you a detailed, step-by-step process that maps cleanly to the broader NIST Cybersecurity Framework. If your company operates in a regulated industry or has federal compliance on the roadmap, NIST is the natural starting point.
ISO/IEC 27005
ISO/IEC 27005 is the international standard built specifically for information security risk management. It’s designed to complement ISO/IEC 27001, and if you’re pursuing that certification or selling to international enterprise customers who expect it, ISO 27005 is the right framework to use. It requires more upfront structure than NIST SP 800-30, but the rigor pays off in audit credibility.
ISACA COBIT
COBIT takes a broader governance view and is popular with larger organizations, aligning IT risk to business strategy. For most early-stage startups, it’s more framework than you need. NIST or ISO 27005 will get you further, faster. (We’d also argue COBIT is more fun to say than it is to implement, but that’s a separate conversation.) See ISACA’s COBIT resources if you want to evaluate it for yourself.
Your choice will come down to your industry, your compliance requirements, and where you are in your security maturity. If you’re not sure, reach out: it’s one of the first things we help clients sort out. The good news is that the six-step process below works across all three.
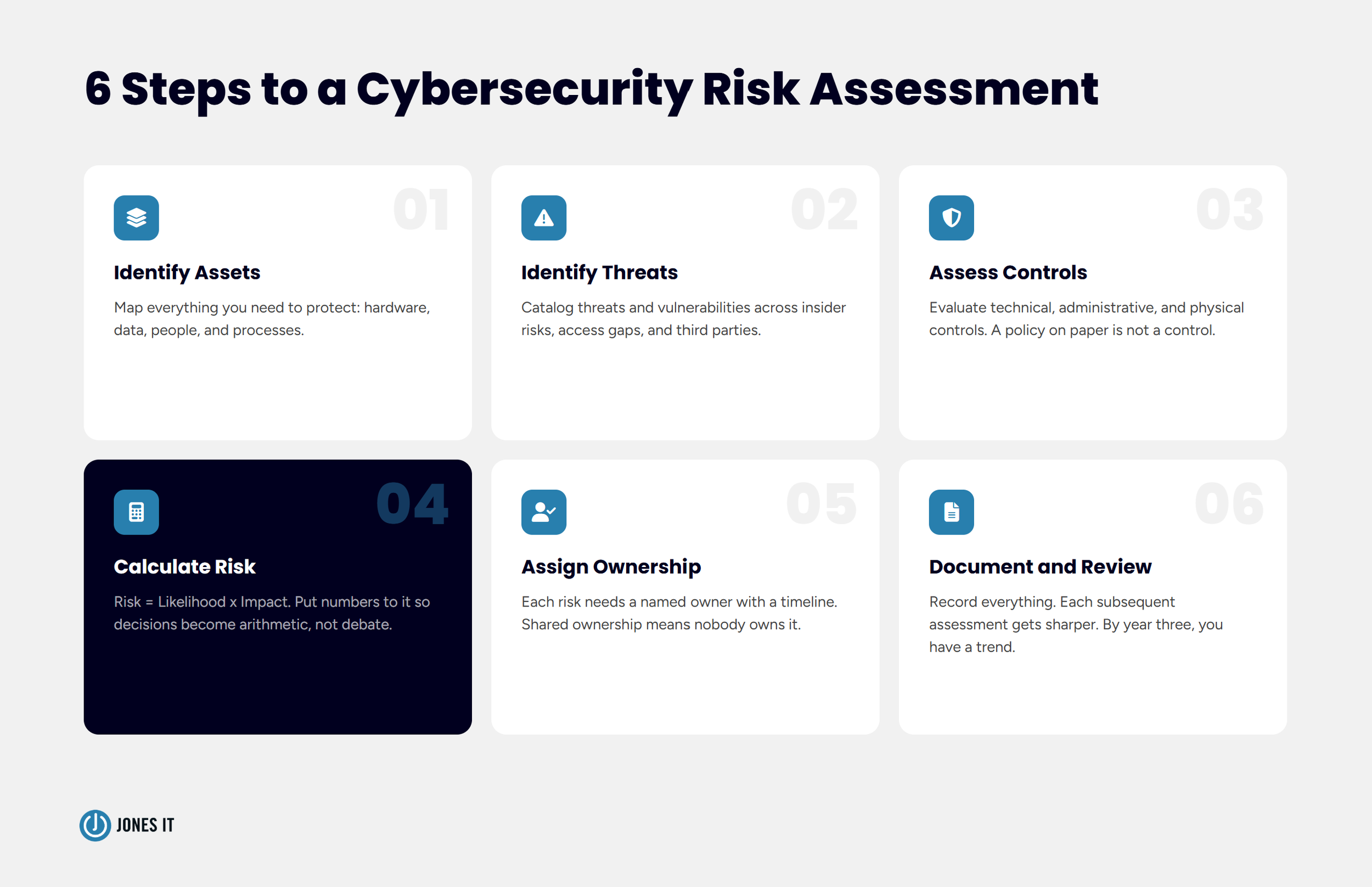
6 Steps to Perform a Cybersecurity Risk Assessment
A risk assessment can be applied to any system, application, or process in your organization. Scope matters here: trying to assess everything at once is usually too broad to be actionable, and you end up with a document so long that nobody reads it. We typically recommend starting with the systems and data that would cause the most damage if compromised, then expanding the scope in subsequent assessments.
1. Identify Your Assets
Start by building a complete inventory of what you need to protect. Assets are not just hardware, though hardware is in there. They include the data your systems process, the people who operate those systems, and the business processes that depend on them. If it would hurt to lose it, it’s an asset.
For each asset, establish its value: financial value, business importance, and regulatory weight. Some useful questions to work through:
What internal and external interfaces does this asset have?
What kind of data flows through it, and how sensitive is that data?
Who are the users, and which vendors have access?
What compliance requirements apply to this asset?
This inventory becomes the foundation for everything that follows. It also tends to surface surprises: systems still running that nobody thought about, vendors with access that was granted two product cycles ago and never reviewed, data sitting in places it absolutely should not be. We’ve seen all of it. It’s not a reflection on any particular team; it’s just what happens when companies grow fast without a systematic way to track what they’ve built.
2. Identify Threats and Vulnerabilities
A threat is anything that could exploit a weakness in your systems to cause harm. A vulnerability is the weakness itself. You need both: a threat without a vulnerability isn’t a real risk, and a vulnerability with no plausible threat doesn’t need to top your list.
Ransomware and external attackers are real threats, and we’re not minimizing them. But statistically, the most common and costly threats tend to be less dramatic:
Insider threats, whether malicious or just careless.
Unauthorized access from stale credentials or over-provisioned accounts (see: our fintech client above).
Data misuse by authorized users.
Human error: accidental deletion, misconfiguration, misdirected email.
Physical loss of a device.
Third-party and supply chain exposure.
Vulnerabilities show up through security audit reports, penetration testing, configuration reviews, and vendor disclosures. The goal is not to address every vulnerability you find (you’ll go mad trying). The goal is to identify which vulnerabilities are most exposed to the threats that matter most to your specific business.
3. Assess Your Current Controls
Before you can calculate how much risk you’re actually carrying, you need an honest picture of what’s already protecting you. This step maps your existing security controls against the threats and vulnerabilities you’ve identified.
Controls fall into three buckets:
Technical controls: MFA, encryption, MDM, endpoint detection and response, intrusion detection systems.
Administrative controls: access review policies, security awareness training, incident response plans, vendor management procedures.
Physical controls: office access badges, video surveillance, device lock policies, and clean desk practices.
The critical distinction here: you’re not just cataloging what controls exist. You’re evaluating whether they’re actually working. A policy that lives in a Google Doc but isn’t enforced or trained on is not a control. It’s a checkbox. There’s a meaningful difference, and auditors know it.
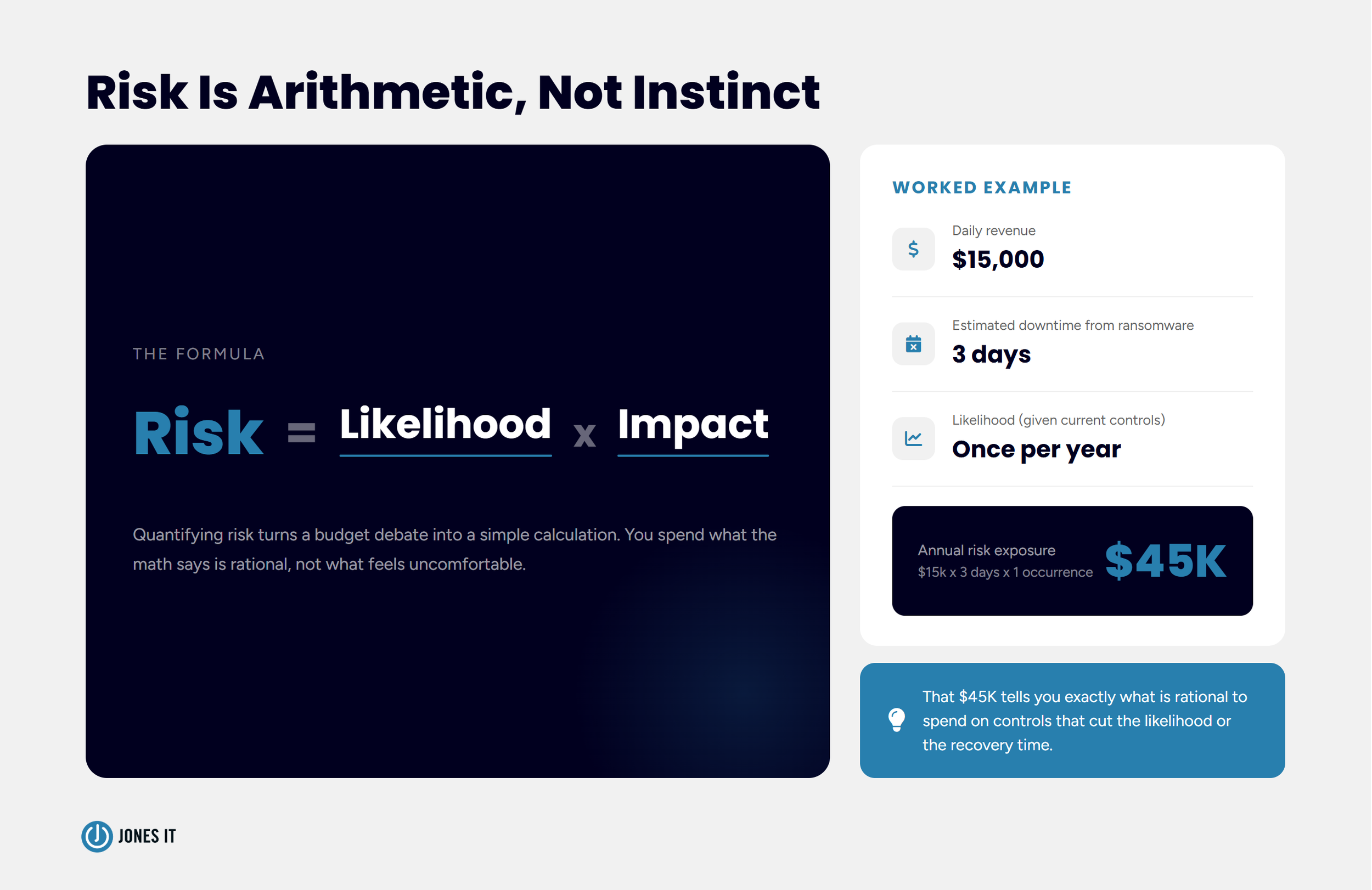
4. Calculate the Risk
Risk is not just a feeling. It can be quantified, and doing so changes the conversation in useful ways. The formula is simple:
Risk = Likelihood x Impact
Here’s a concrete example. Your average daily revenue is $15,000. A ransomware attack takes your systems offline for three days before you can restore from backup. Financial impact: $45,000. You assess the likelihood of that threat materializing at roughly once per year, given your current controls. Annual risk exposure from that single threat: $45,000. That number tells you what it’s rational to spend on controls that reduce either the likelihood or the recovery time. Suddenly, it’s not a budget debate, it’s arithmetic.
Not all risk is financial, of course. A breach of customer PII carries reputational damage, regulatory penalties, and customer churn that resist clean quantification. Attach a monetary estimate anyway, even a rough one, and use those estimates to prioritize. Perfect numbers are not the goal. Consistent, comparable numbers are.
5. Assign Ownership
A risk without an owner is a risk that sits on a list forever. For each identified threat, assign a specific person responsible for the mitigation plan. Not a team. Not a department. A person. Individual ownership creates accountability; shared ownership creates ambiguity about whose problem it actually is.
Mitigation plans vary a lot in complexity. Some risks can be addressed in an afternoon: rotating stale credentials, enabling MFA on a system that slipped through, and removing a vendor’s access. Others involve real projects: a new MDM rollout, network segmentation, and an incident response plan built from scratch. Both types need owners and timelines, or they don’t move.
6. Document and Review
Create a formal record of your assessment: every asset, every threat, every vulnerability, your risk calculations, your mitigation plans, and who owns each one. This document is not just for compliance auditors, though it will make their lives considerably easier. It’s a management tool that tracks your progress over time and makes subsequent assessments substantially faster.
Your first assessment will have gaps. You’ll rely on estimates where you don’t have precise data. That’s not a failure; it’s the nature of a first pass. Each subsequent assessment gets sharper, incorporating real incident data, updated threat intelligence, and a cleaner picture of your environment. By year two, you’re comparing against a baseline. By year three, you have a trend. That’s when the process really starts paying for itself.
Next Steps: Turning Your Risk Assessment Into a Security Program
Finishing a cybersecurity risk assessment is not the finish line. It’s the starting point for a security program that actually reflects how your business works. Once you have a documented risk picture, the work is building the controls and processes that reduce your highest-priority exposures over time.
For companies on a compliance path, your assessment results feed directly into certification. ISO/IEC 27005 and NIST SP 800-39 both use risk assessment outputs as inputs to broader information security management systems. We’ve worked with clients across SoMa, Mission Bay, and the Financial District through exactly this process. Certification is achievable without swallowing your engineering calendar whole, but it requires a credible risk assessment to build from. Check out our cybersecurity and compliance services, or if you’re earlier in the journey, our Compliance Kickstarter Program is designed for exactly that stage.
If you’d like to talk through where your company sits and what a practical assessment process would look like for your environment, reach out to us. We’ve helped companies at every stage of this, from first-time assessments to full compliance program buildouts, and we’re happy to start with a conversation.