In this blog post, we dive into the topic of IT Service Management (ITSM), its benefits, and the various processes involved in effective and efficient service delivery.
In this blog post, we will dive deeper into not just device lifecycle management but IT asset management (ITAM) as a whole in remote and hybrid work environments.
This blog post covers the role of IT Asset Management (ITAM), what ITAM involves, how it works, the benefits of ITAM, and its key features.
In this blog post, we take a look at proxy servers, covering topics such as the definition of a proxy server, how they work, types of proxy servers, when and why to use proxy servers, and how to set it up.
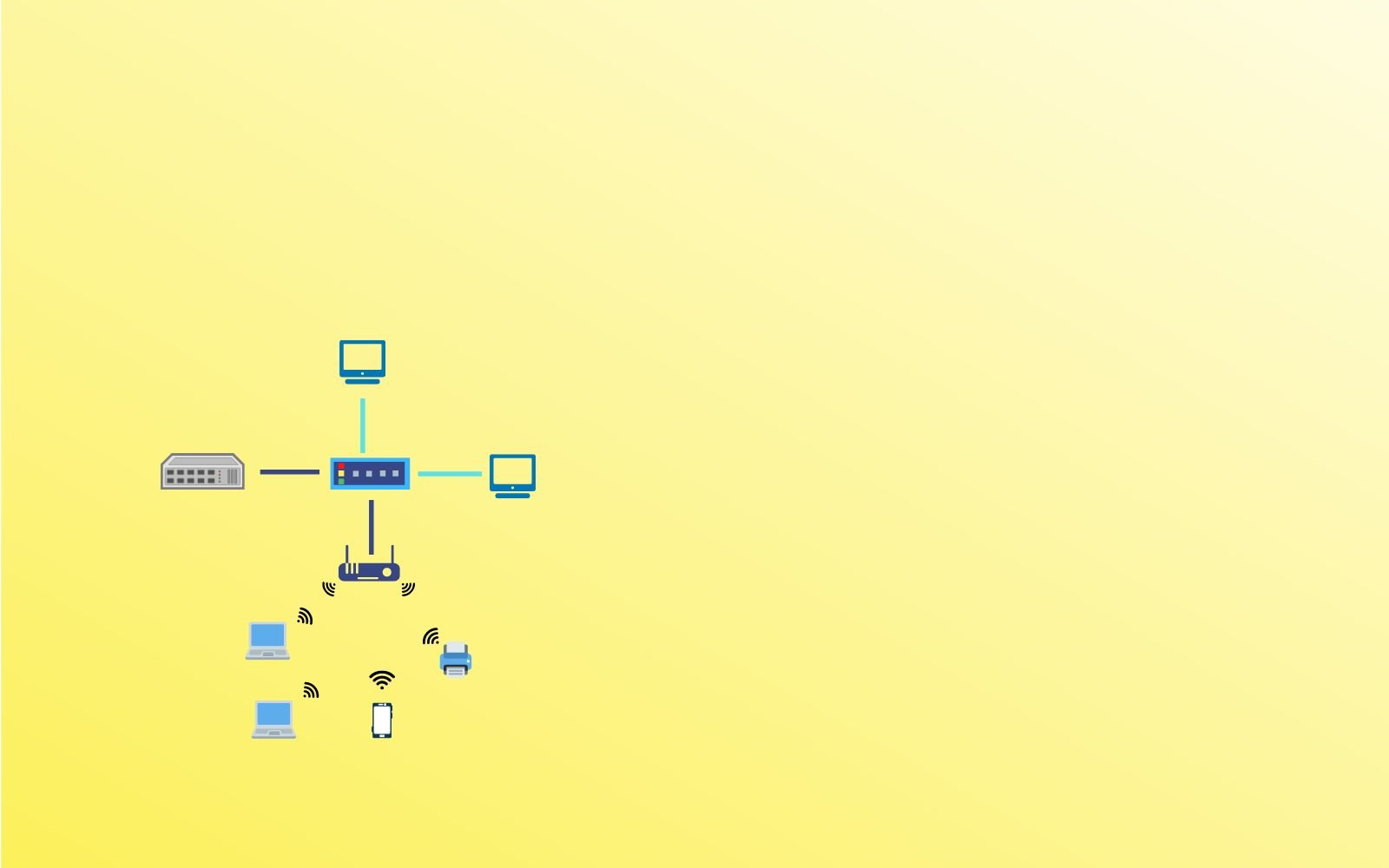
This blog post shares tips that not just help you solve common wireless network issues but also get the best performance out of your wireless network.
In this blog post, we introduce you to common networking acronyms and abbreviations with their meaning for ready reference.
In this blog post, I cover the topic of server maintenance including its need, server maintenance frequency, types, and best practices.
This blog post discusses four key challenges organizations face when transitioning to a fully remote or hybrid work environment.
In this blog post, I am going to share ten server security best practices ranging from physical security and firewalls to intrusion detection and security audits.
This blog post dives into the topic of IT inventory and asset management, its importance, how it works, different types of inventory management, and how to inventory IT assets.
In this blog post, I discuss IT support in detail including what IT support is, what IT support technicians do, how businesses benefit from such services, and how to choose the right vendor for your IT needs.
This blog post covers device lifecycle management, its importance, benefits, and the role it plays in facilitating global employee mobility.
In this blog post, I answer what an IT strategy is and share a step-by-step process for creating an effective IT strategy for your organization.
This blog post talks about Data Loss Prevention (DLP), how it works, its importance, and how to implement a DLP program for your business.
This blog post shares network security best practices that employees need to follow so that they can continue working remotely securely.
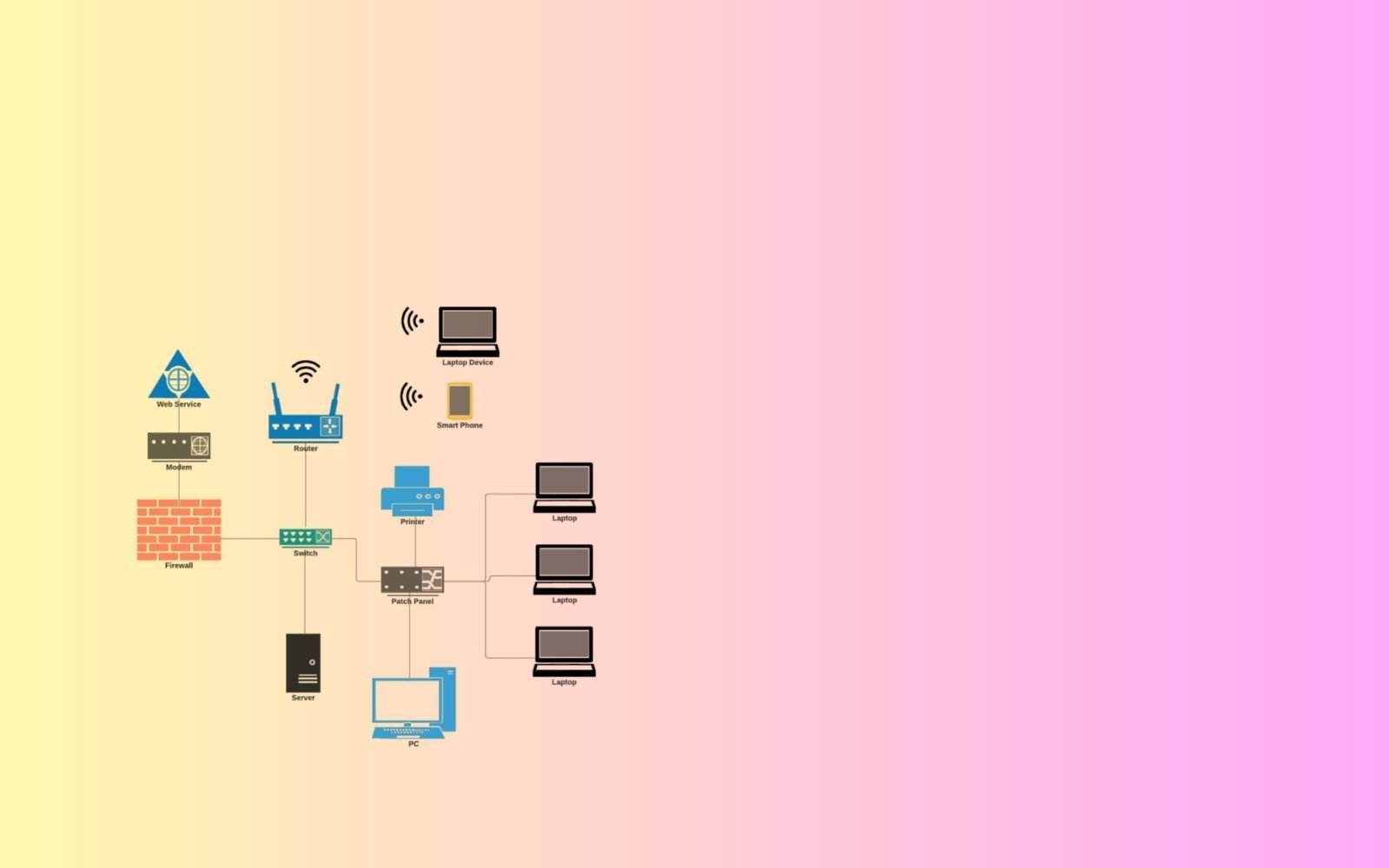
This blog post is a step-by-step guide on how to configure a network server. It covers steps from setting up user accounts to setting up shared resources to testing the server.
In this blog post, I discuss the challenges in Networking For IoT, including device management, scalability, interoperability, and how to set up and secure an IoT network.
In this blog post, we will discuss the types of servers based on their platform and ownership, namely cloud servers, virtual servers, and shared and dedicated servers.
In this blog post, I share with you 12 Windows 11 tips and tricks that will help you become more organized and maximize your efficiency.